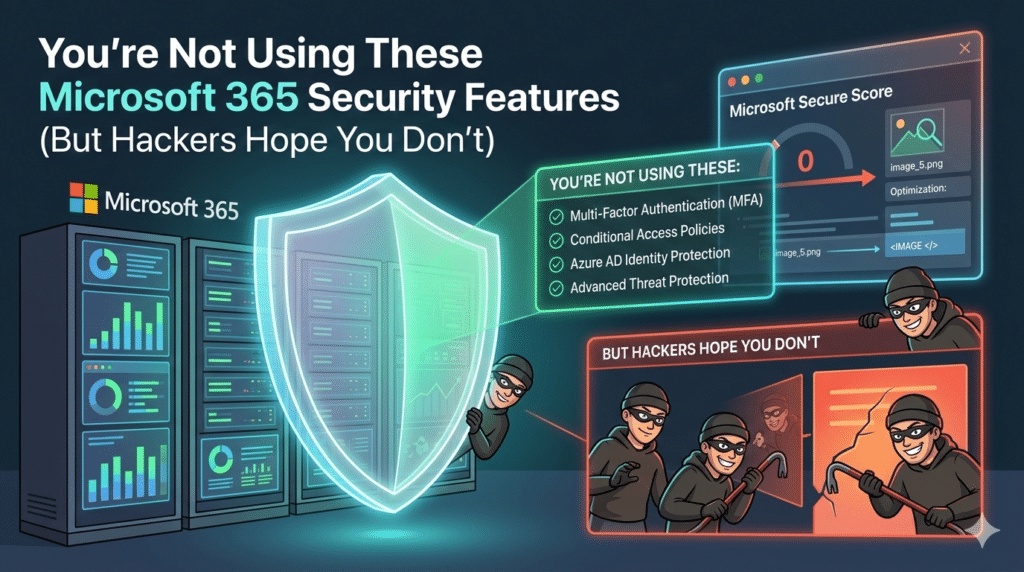
Microsoft 365 security features are built-in tools designed to protect your email, files, users, and devices from cyber threats. The problem? Many businesses never turn them on.
If you’re using Microsoft 365 for email, file sharing, and collaboration, you already have access to powerful security controls. But default settings alone are not enough to stop phishing, ransomware, or account takeovers.
Hackers rely on one thing: misconfigured environments.
Here are the Microsoft 365 security features you should enable right now.
1. Multi-Factor Authentication (MFA)
If you turn on only one feature, make it this one.
Multi-factor authentication requires users to verify their identity using something beyond a password, such as:
- A mobile authentication app
- A text message code
- A biometric scan
Why it matters:
Over 80% of breaches involve compromised passwords. MFA dramatically reduces the chance of unauthorized access, even if login credentials are exposed.
Pro tip: Avoid SMS when possible. Use the Microsoft Authenticator app for stronger protection.
2. Conditional Access Policies
Conditional Access allows you to control who can log in, from where, and under what conditions.
You can:
- Block logins from high-risk countries
- Require compliant devices
- Restrict access outside business hours
- Enforce MFA only under certain risk levels
This creates intelligent access control instead of blanket permissions.
Hackers often attempt logins from overseas IP addresses. Conditional Access can stop those attempts automatically.
3. Microsoft Defender for Office 365
Email is still the number one attack vector.
Microsoft Defender for Office 365 includes:
- Safe Links (scans URLs in real time)
- Safe Attachments (sandbox testing for files)
- Anti-phishing protection
- Spoof intelligence
These features inspect incoming emails before users click anything.
Without advanced protection, phishing emails can bypass basic spam filters and compromise entire networks.
4. Data Loss Prevention (DLP)
Data Loss Prevention policies monitor and restrict sensitive information.
You can prevent users from:
- Sharing credit card numbers externally
- Sending confidential files outside the organization
- Copying protected information to personal accounts
For businesses handling financial, healthcare, or legal data, DLP is critical for compliance and risk reduction.
5. Audit Logs and Alerts
Microsoft 365 provides detailed audit logging, but many organizations never review it.
Audit logs track:
- Login attempts
- File downloads
- Permission changes
- Admin actions
You can also set up alerts for suspicious behavior, such as:
- Mass file deletions
- Unusual sign-in patterns
- Multiple failed login attempts
Early detection prevents small incidents from becoming full-scale breaches.
6. OneDrive and SharePoint Version History
Ransomware often encrypts files silently.
Version history allows you to:
- Restore previous versions of files
- Recover from malicious edits
- Roll back entire document libraries
This feature acts as a built-in safety net, but only if retention settings are properly configured.
7. Secure Score Monitoring
Microsoft Secure Score gives you a measurable rating of your security posture.
It highlights:
- Recommended improvements
- Risk exposure areas
- Configuration gaps
Think of it as a security checklist that evolves with new threats.
Regular review of Secure Score ensures your Microsoft 365 environment doesn’t become outdated or vulnerable.
Why Default Settings Aren’t Enough
Microsoft 365 is powerful, but it is not automatically hardened.
Many businesses:
- Enable licenses but skip configuration
- Turn on MFA only for admins
- Ignore alert policies
- Assume email filtering is sufficient
Cybercriminals specifically target Microsoft 365 tenants because they know misconfigurations are common.
Security is not about having tools. It’s about using them correctly.
Common Mistakes Businesses Make
- Sharing global admin access with too many users
- Not enforcing password policies
- Failing to back up Microsoft 365 data
- Ignoring sign-in risk alerts
- Allowing unmanaged devices access
Even small gaps create entry points.
How to Strengthen Your Microsoft 365 Security Today
Start with this checklist:
- Enable MFA for all users
- Implement Conditional Access policies
- Turn on Defender for Office 365 protections
- Configure DLP policies
- Review Secure Score monthly
- Set up audit alerts
- Verify backup strategy
If you’re unsure how your environment is configured, run a security review. Many organizations discover weaknesses they didn’t know existed.
Frequently Asked Questions
Is Microsoft 365 secure by default?
It includes strong security tools, but many advanced protections require manual setup and configuration.
Do small businesses really need advanced security settings?
Yes. Small businesses are often targeted because attackers assume weaker defenses.
Is MFA enough to protect my account?
MFA significantly reduces risk, but it should be combined with Conditional Access, Defender protections, and monitoring.
Does Microsoft 365 back up my data automatically?
Microsoft provides retention and versioning, but it is not a full replacement for a dedicated backup solution.
How often should Microsoft 365 security be reviewed?
At minimum, quarterly. Ideally, monthly reviews of Secure Score and sign-in activity are recommended.
Final Thoughts
If you are using Microsoft 365 without reviewing your security settings, you may be more exposed than you realize.
The tools are already there. The real risk is leaving them unused.
Hackers look for easy targets. Turning on these Microsoft 365 security features makes sure your organization is not one of them.
